The recent revelation of a ₹315 crore loan fraud at IDFC First Bank sent shockwaves through the Indian financial market, triggering a 16% stock crash and prompting brokerages like Nomura to slash target prices and demand forensic audits. While the financial analysis focuses on balance sheets and credit risk, a more insidious threat vector lies exposed within the bank's—and indeed, every corporation's—operational backbone: the standardized, predictable, and high-volume world of mandatory corporate filings. This 'compliance churn' of EGM results, postal ballots, earnings call transcripts, and board meeting disclosures represents a fertile, yet overlooked, ground for insider threats and sophisticated fraud.
The Paper Trail as a Weapon: Blending In with the Noise
Corporate life is governed by a relentless calendar of disclosures. As seen in recent announcements, Jolly Plastic Industries publishes EGM voting results, Solar Industries India finalizes a postal ballot for director appointments, and Rane (Madras) Ltd. releases its quarterly earnings call transcript. Each event is routine, expected, and follows a well-worn procedural path. This normalization is precisely its vulnerability. For a malicious insider or an external actor with internal collusion, this flood of legitimate documents and processes provides perfect camouflage.
In a scenario like the IDFC First Bank fraud, where fraudulent letters of undertaking and guarantees were allegedly processed, the attack didn't necessarily require hacking a firewall. It likely exploited the trusted internal pathways used for genuine compliance activities. An attacker familiar with the timing of board meetings, the format of internal approval memos, or the workflow for processing guarantees could insert fraudulent transactions into the system, making them appear as just another item in the endless 'paper trail.' The operational security (OpSec) around these routine financial and governance processes is often minimal, focused more on regulatory accuracy than on malicious intent.
The Insider Risk Amplified by Predictability
The predictability of corporate events creates a roadmap for social engineering and reconnaissance. A publicly available earnings call transcript (like Rane Madras's Q3 FY26 transcript) provides a wealth of information: key executive names, departmental priorities, operational challenges, and financial terminology used internally. This data is gold for crafting a highly targeted phishing email or a vishing (voice phishing) call. An attacker could pose as a member of the legal team right after an EGM, requesting 'urgent verification' of details, leveraging the recent real event to add credibility.
Similarly, the process for a postal ballot or share allotment involves specific departments, deadlines, and document templates. An insider looking to commit fraud or exfiltrate data can time their actions to coincide with these peaks of legitimate activity, knowing that oversight may be strained and anomalous behavior might be lost in the noise. The 'compliance churn' creates periods of focused distraction, where the organization's eyes are on meeting regulatory deadlines, not on detecting subtle deviations in process.
From Financial Fraud to Market Manipulation
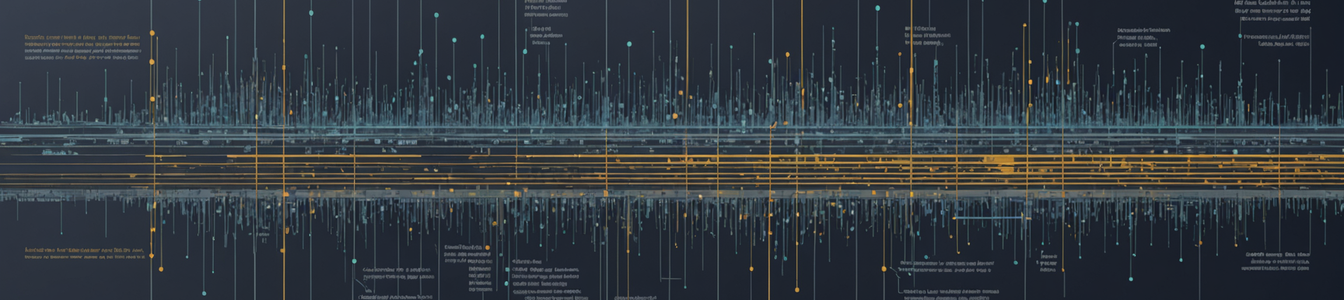
The risk extends beyond direct theft. This ecosystem of filings can be weaponized for market manipulation. Controlled, selective leaks of information from upcoming but unreleased earnings calls or board meeting minutes could be used for insider trading. More subtly, creating forgeries of routine documents—like a fake EGM result announcement hinting at unexpected leadership changes—could be released to manipulate a company's stock price briefly but profitably. The speed and automated nature of modern financial news aggregation (as seen with platforms like ScanX.Trade that disseminate these filings) mean such false information could gain temporary traction before being debunked.
Mitigating the Threat: Evolving Data Governance for the Compliance Era
Addressing this vulnerability requires a paradigm shift in data governance and insider risk programs. Compliance processes must be re-evaluated through a security lens.
- Process-Centric Threat Modeling: Instead of just modeling threats against IT systems, organizations must model threats against key business processes like 'guarantee issuance,' 'EGM resolution execution,' or 'earnings release.' Identify where trust is inherent and where verification is assumed.
- Enhanced Transaction & Behavioral Anomaly Detection: Security tools should monitor for anomalies within legitimate workflows. For example, detecting a guarantee processed outside the normal cycle following a board meeting, or an access request for ballot data from an unusual department.
- Multi-Factor Verification for High-Impact Routines: For critical compliance-driven actions (e.g., filing results with a stock exchange, releasing allotment notices), implement a dual-control or multi-factor approval mechanism that is separate from the standard operational workflow.
- Security Awareness for Non-IT Staff: Train legal, company secretarial, and finance teams on these specific threats. They are the frontline for these processes and must recognize signs of social engineering attempts that leverage their routine work.
- Digital Signatures and Integrity Checks: Ensure all published filings and internal compliance documents use cryptographically verifiable digital signatures and hashes to prevent tampering and forgeries.
The IDFC First Bank fraud is a stark reminder that the most significant risks often reside in the business processes we consider mundane and safe. In an age of digital compliance, the 'paper trail' is no longer just an audit requirement; it's a digital attack surface. By integrating security into the very heart of governance and compliance operations, organizations can transform their 'compliance churn' from a vulnerability into a verified, secure backbone of corporate integrity.
Comentarios 0
Comentando como:
¡Únete a la conversación!
Sé el primero en compartir tu opinión sobre este artículo.
¡Inicia la conversación!
Sé el primero en comentar este artículo.