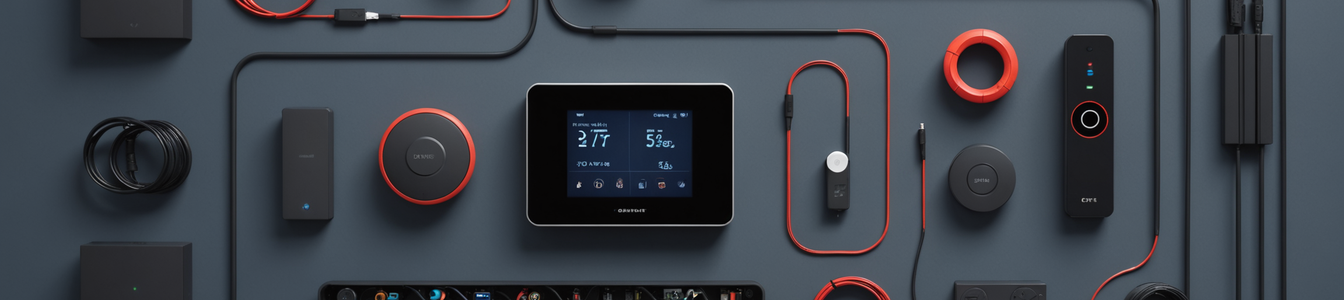
The Internet of Things (IoT) landscape is evolving beyond convenience and automation into the realm of behavioral modification. A new generation of devices is emerging that employs hardware-level mechanisms to physically enforce or incentivize specific user behaviors. From sensors that block social media access until physical exercise is detected to smart home systems that autonomously control environmental factors, these 'autocontrol' gadgets represent a paradigm shift with profound implications for cybersecurity, data privacy, and digital autonomy.
The Hardware Enforcement Mechanism
Unlike traditional software-based solutions—parental control apps or website blockers that run at the application layer—these devices implement restrictions at the hardware or firmware level. This creates a more fundamental barrier to circumvention. For instance, a device might physically interrupt network connectivity to specific services or control power supply to certain appliances based on predefined behavioral criteria. The intelligent radiator fan tested in German markets, which autonomously adjusts heating based on occupancy and weather data to optimize energy savings, exemplifies this trend toward hardware-enforced efficiency behaviors, albeit with less direct personal coercion.
Convergence with Health Monitoring
The security implications become particularly acute when behavioral enforcement converges with health monitoring capabilities. The recent activation of hypertension notification features in Apple Watch devices following regulatory approval in markets like Brazil illustrates this intersection. When a device that can detect medical conditions also possesses the capability to enforce behaviors—potentially restricting access to content or services based on health metrics—it creates unprecedented privacy and control dilemmas. The biometric and behavioral data collected creates highly sensitive profiles that could be exploited if compromised.
Primary Security and Privacy Risks
- Bypass Vulnerabilities and Attack Surfaces: Any hardware-enforced control mechanism becomes a target for bypass. Security researchers must consider vulnerabilities in the sensor systems (e.g., fooling motion detectors), the enforcement mechanisms (e.g., hijacking network interruption modules), and the decision logic. A compromised 'autocontrol' device could be turned into a tool for denial-of-service against the user or manipulated to remove beneficial restrictions.
- Data Sovereignty and Behavioral Profiling: These devices typically collect granular behavioral data—when users exercise, work, relax, or even their physiological responses. The aggregation of this data by manufacturers or third parties raises critical questions about data ownership, usage transparency, and cross-border data flows. In jurisdictions with strong data protection laws like Brazil's LGPD or the EU's GDPR, the legal classification and handling of such 'behavioral biometric' data remain ambiguous.
- Normalization of External Hardware Control: The most concerning precedent may be sociological rather than purely technical. The acceptance of hardware that physically controls personal device functionality, especially when manufactured by third parties, erodes the principle of user sovereignty over devices. It creates a market for increasingly coercive technologies and could lead to insurance or employer-mandated 'productivity' or 'wellness' devices that enforce behaviors.
- Supply Chain and Firmware Integrity: The security of these devices depends heavily on secure boot processes, signed firmware updates, and protected hardware communication channels. A compromised update server or malicious insider in the supply chain could push firmware that alters behavioral parameters, enforces malicious restrictions, or exfiltrates sensitive data.
- Lack of Standardization and Security Frameworks: This product category is emerging faster than security standards can develop. There are no established frameworks for vulnerability disclosure, secure design principles, or independent security verification specific to behavior-modifying IoT hardware.
The Road Ahead for Cybersecurity Professionals
For the cybersecurity community, this trend demands several responses:
- Research Focus: Increased scrutiny on the hardware security architecture of these devices, including side-channel attacks against sensors and fault injection attacks against enforcement circuits.
- Penetration Testing Methodologies: Developing specialized pentesting frameworks for behavioral IoT devices that go beyond network and application testing to include physical sensor spoofing and control logic manipulation.
- Policy and Standards Advocacy: Engaging with regulators and standards bodies to establish security baselines for devices that exert behavioral control, emphasizing transparency, user override capabilities, and data minimization.
- User Education: Informing consumers about the long-term privacy and security implications of adopting hardware-enforced behavior modification, distinguishing between genuine wellness tools and potentially coercive surveillance products.
The emergence of 'autocontrol' IoT devices represents a significant inflection point. While offering potential benefits for productivity and health, they introduce novel risks that challenge traditional cybersecurity models focused on confidentiality, integrity, and availability. The core addition—user autonomy—must now be explicitly defended. As these devices proliferate, the cybersecurity community's role in analyzing their vulnerabilities, advocating for secure design, and protecting users from both technical exploits and societal overreach will be crucial. The hardware that controls behavior must itself be controlled by robust security principles.
Comentarios 0
Comentando como:
¡Únete a la conversación!
Sé el primero en compartir tu opinión sobre este artículo.
¡Inicia la conversación!
Sé el primero en comentar este artículo.