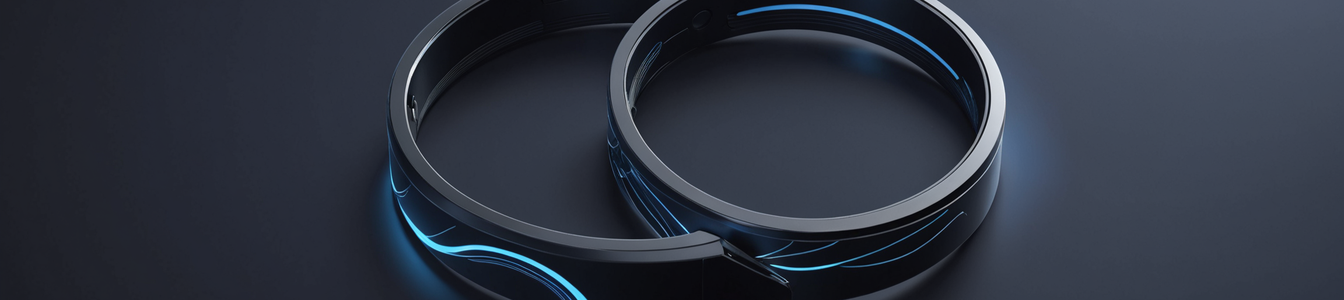
The promise of the "quantified self" has evolved from simple step counting to a continuous, intimate stream of biometric data. Wearable Internet of Things (IoT) devices, epitomized by sophisticated trackers like the Oura Ring, now claim to diagnose stress levels, predict illness through subtle physiological changes, and measure "readiness" for daily tasks. This data pipeline, however, is built on a foundation of consumer-grade security, creating a ticking time bomb for privacy and creating new vectors for corporate and institutional manipulation. For cybersecurity professionals, this represents a critical convergence point where data privacy, biometric security, and the Internet of Medical Things (IoMT) collide with insufficient safeguards.
From Fitness to Diagnosis: The Expanding Data Footprint
Modern wearables have transcended their origins. They are no longer mere pedometers but bio-surveillance platforms. Devices like the Oura Ring collect heart rate variability (HRV), skin temperature, blood oxygen saturation (SpO2), and sleep architecture data. Algorithms then extrapolate this into metrics for stress, recovery, and even potential sleep apnea. This shift from tracking to diagnosing places these devices firmly in the health tech (IoMT) realm, yet they lack the rigorous security and privacy standards mandated for traditional medical devices under regulations like HIPAA in the US or the GDPR's provisions on health data in the EU.
The security model is often that of a consumer gadget: data is streamed to a smartphone via Bluetooth (often with historically vulnerable protocols like BLE 4.2), synced to a cloud platform, and processed. The chain of custody is long and fraught with potential weak links—from device theft and unauthorized Bluetooth pairing to insecure cloud APIs and third-party data sharing agreements obscured in lengthy privacy policies.
The Liability Shift: When Personal Data Becomes a Corporate Tool
The true risk emerges when this intimate data pipeline intersects with other systems. Two areas are of paramount concern:
- Workplace Wellness and Performance Management: Employers, incentivized by lower insurance costs and higher productivity, are increasingly incorporating wearable data into corporate wellness programs. What begins as an optional challenge can morph into a de facto requirement, with data on sleep and "readiness" used to gauge employee resilience or flag "high-risk" individuals for managerial scrutiny. A data breach in this context doesn't just leak steps taken; it exposes an employee's chronic stress patterns, potential undisclosed health conditions, and even lifestyle choices, opening the door to discrimination and biased performance evaluations.
- Insurance and Actuarial Models: Life, health, and disability insurers have a keen interest in predictive health data. While currently often based on voluntary sharing programs, the line between incentive and coercion is thin. Biometric data from wearables could be used to adjust premiums, deny coverage, or create deeply personalized—and potentially exclusionary—risk models. A vulnerability leading to the exfiltration of such a dataset would be a goldmine for fraudsters and a catastrophe for individuals, enabling targeted scams or blackmail based on health vulnerabilities.
The Cybersecurity Imperative: Securing the Biometric Lifecycle
For security teams, the challenge is multifaceted. The attack surface includes the physical device, the mobile application, the communication protocols, the cloud infrastructure, and all downstream data processors. Key focus areas must be:
- End-to-End Encryption (E2EE): Data must be encrypted at rest on the device, in transit, and at rest in the cloud. Tokenization should be used where possible to anonymize data during processing.
- Strong Device Identity and Authentication: Preventing spoofing and unauthorized device pairing is critical. Implementing hardware-backed secure elements for key storage is a best practice moving beyond software-only solutions.
- Data Minimization and Sovereignty: Companies should collect only what is absolutely necessary and allow users clear, granular control over where their data is stored and processed. The principle of data sovereignty is paramount for cross-border data flows of sensitive biometric information.
- Transparent Breach Notification: Given the sensitivity of the data, regulations must mandate swift, clear notification to users in the event of a breach, detailing exactly what biometric data was compromised.
Conclusion: Reclaiming the Narrative
The backlash against the quantified self is not a rejection of technology but a demand for responsibility. The intimate biometric data generated by IoT wearables is a new class of asset that is also a profound liability if mishandled. The cybersecurity community has a pivotal role to play in advocating for and implementing architectures that treat this data with the gravity it deserves. Without proactive security-by-design principles, robust encryption, and strong legal frameworks, the very tools promising personal health empowerment risk becoming instruments of surveillance, discrimination, and unprecedented personal risk. The time to secure the biometric future is now, before the data pipeline becomes a weaponized asset.
Comentarios 0
Comentando como:
¡Únete a la conversación!
Sé el primero en compartir tu opinión sobre este artículo.
¡Inicia la conversación!
Sé el primero en comentar este artículo.