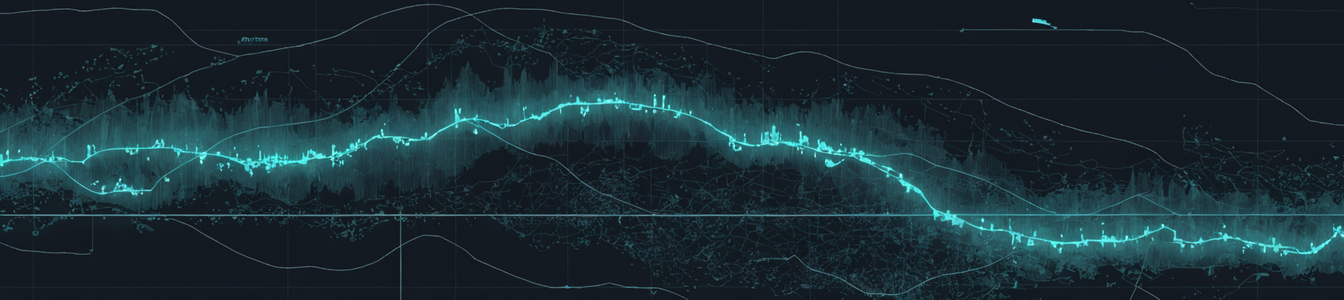
The global maritime supply chain is undergoing a radical, real-time transformation. Faced with persistent kinetic threats in established geopolitical chokepoints, commercial shipping is not just slowing or stopping—it is inventing new pathways. Our investigation confirms the active development and use of unofficial 'shadow maritime corridors,' ad-hoc shipping lanes created to bypass high-risk zones like the Strait of Hormuz. This emergent behavior, a direct response to conflict, is rewriting global trade routes on the fly and exposing a critical, unaddressed frontier in cyber-physical security.
The Emergence of Shadow Corridors
The concept is simple in theory, perilous in practice. When a primary artery is blocked or deemed too dangerous, traffic finds a way around. Reports now indicate that multiple vessels, including Indian-flagged ships, are actively circumventing traditional routes near Iran. A prime example is the LPG tanker Green Sanvi, which recently completed a transit carrying 46,650 metric tons of liquefied petroleum gas to India via an alternative path that avoided the most contested waters of the Hormuz Strait. This is not an isolated deviation but a signal of a systemic shift. These shadow corridors are characterized by their lack of formal designation, inconsistent monitoring, and reduced naval patrol presence. They are the supply chain's improvisation, a testament to logistical resilience but also a glaring vulnerability.
The Amplified Cyber-Physical Threat Landscape
Operating in these uncharted, less-regulated spaces significantly elevates risk. The cybersecurity implications for vessels traversing shadow corridors are profound and multifaceted:
- Increased Targeting for Cyber-Physical Attacks: Ships on predictable, major routes benefit from a degree of safety in numbers and established monitoring. A vessel on an ad-hoc route is more isolated, making it a preferable target for hostile actors seeking to disrupt cargo (especially critical energy or data cable-laying ships) without immediate detection. The recent report of a significant Iranian strike on a U.S. Embassy facility in Saudi Arabia underscores the heightened kinetic threat environment in the region, which often includes a complementary cyber dimension.
- Vulnerability to Navigation System Exploits: Reliance on Global Navigation Satellite Systems (GNSS) like GPS and Automatic Identification Systems (AIS) is absolute in open water. In shadow corridors, the risk of GNSS spoofing or jamming increases dramatically. A hostile state or criminal group could manipulate a ship's perceived position, luring it into territorial waters for seizure or grounding, or creating collisions to cause logistical chaos. The lack of dense, normal maritime traffic makes anomaly detection harder for onboard systems and shore-based security teams.
- Compromised Operational Technology (OT) Security: Maritime OT—the systems that control propulsion, steering, cargo management, and ballast—is often legacy infrastructure with known vulnerabilities. In a high-threat zone, the incentive for actors to exploit these vulnerabilities rises. An attack that cripples a ship's engines or steering in a remote, alternative corridor could have delayed response times for emergency assistance, turning a cyber incident into a major environmental and economic disaster.
- The Intelligence and Surveillance Gap: Shadow corridors exist in intelligence-poor environments. Threat intelligence feeds, maritime domain awareness pictures, and even piracy reporting are tuned to major routes. A security operations center (SOC) for a shipping company may have limited visibility into the unique digital or physical threats emerging along these improvised paths, creating a dangerous blind spot.
Implications for Cybersecurity and Risk Management
For cybersecurity leaders in logistics, energy, and insurance, the rise of shadow corridors demands an urgent strategic pivot. Traditional risk assessments based on fixed chokepoints are now incomplete. The attack surface has become fluid and dynamic.
- Dynamic Risk Modeling: Security teams must move from static maps to adaptive models that can incorporate real-time geopolitical alerts and predict likely emergent routes. Risk scoring must now follow the asset, not just the planned route.
- Hardening the Mobile Asset: There is a non-negotiable need to accelerate programs for maritime OT hardening. This includes network segmentation, robust anomaly detection for ICS/SCADA systems, and ensuring secure, redundant communication channels for vessels operating outside standard lanes.
- Enhanced Maritime Threat Intelligence: Intelligence gathering must expand to monitor signals and indicators of compromise (IoCs) related to secondary shipping lanes and unusual maritime behavior. Collaboration between commercial threat intel firms and national maritime agencies becomes even more critical.
- Supply Chain Cyber Resilience: Cargo owners must pressure their logistics partners for transparency on route deviations and the specific cybersecurity measures in place for vessels using alternative corridors. Insurance underwriters will likely begin pricing policies based on a vessel's cybersecurity posture and its intended route's 'shadow' risk factor.
Conclusion: The New Normal of Fluid Geography
The creation of shadow maritime corridors is a stark indicator of a fragmenting global system. It demonstrates adaptability but also reveals a dangerous gap in security governance. As geography becomes fluid in the face of conflict, cybersecurity can no longer be a static, port-centric concern. It must become as mobile and adaptive as the ships and routes themselves. Protecting the data, control systems, and navigation integrity of vessels on these unofficial pathways is no longer a niche maritime IT issue—it is a foundational component of global economic and national security. The race is on to secure these emergent lifelines before adversaries map and exploit them first.
Comentarios 0
Comentando como:
¡Únete a la conversación!
Sé el primero en compartir tu opinión sobre este artículo.
¡Inicia la conversación!
Sé el primero en comentar este artículo.