India's rapid digitization of public services—from agriculture and logistics to urban governance and MSME financing—is creating systemic cybersecurity vulnerabilities as technological adoption out...
India's rapid digitization of public services—from agriculture and logistics to urban governance and MSME financing—is creating systemic cybersecurity vulnerabilities as technological adoption out...
A confluence of recent reports on education and workforce trends paints a concerning picture for the future of the cybersecurity talent pipeline. Analysis reveals a growing misalignment between how st...

A sophisticated phishing campaign is actively targeting PayPal users across German-speaking regions, employing deceptive emails that falsely claim account restrictions. The operation uses convincing s...
The cybersecurity threat landscape is undergoing a profound shift, moving from purely technical exploits to sophisticated attacks targeting fundamental human psychology and societal trust. This invest...
The UK government is proposing new legislation that could effectively ban VPN access for minors and impose stricter controls, sparking significant backlash from privacy advocates and the cybersecurity...

A concerning trend is emerging in the IoT landscape where manufacturers are placing core functionality, advanced automations, and even critical security features behind subscription paywalls. This pra...

A disturbing global pattern is emerging where intimate data—private videos, personal messages, and sensitive communications—is being weaponized for blackmail, reputational destruction, and politic...
India's Unique Identification Authority (UIDAI) has launched a new mobile application that centralizes Aadhaar digital identity services on smartphones, enabling features like quick verification, sele...

A recent fatal aviation crash in India has exposed profound systemic vulnerabilities in the oversight of critical transportation infrastructure, with direct parallels to cybersecurity governance failu...
A sophisticated wave of phishing campaigns is targeting streaming platform subscribers worldwide, exploiting the massive user bases and payment data concentrated in services like Netflix, Prime Video,...

The consumer authentication landscape is experiencing divergent strategic shifts. Amazon has announced the shutdown of its Amazon One palm recognition service in retail stores, marking a retreat from ...
Modern Security Operations Centers (SOCs) are facing a perfect storm of hardware-level vulnerabilities and semiconductor supply chain disruptions, creating unprecedented challenges for enterprise secu...
A new category of IoT devices that physically enforce user behavior through hardware mechanisms is raising significant security and privacy concerns. These 'autocontrol' gadgets, ranging from social m...

India's Economic Survey 2026 outlines a fundamental transformation in regulatory philosophy, shifting from coercive enforcement to a data-driven, behavioral compliance model centered on the NUDGE fram...

Enterprise cloud security is undergoing a fundamental shift driven by two converging technological frontiers. On the cryptographic front, Attribute-Based Encryption (ABE) is emerging as a powerful fra...
A global surge in artificial intelligence investment is creating what security experts call 'systemic security debt,' as corporations prioritize rapid deployment over robust security frameworks. Major...

A global wave of cryptocurrency regulation is creating an unexpected consequence: a proliferation of new attack surfaces and security vulnerabilities. As jurisdictions from the EU to Russia and the UA...

As 'agentic AI' systems increasingly govern workplace decisions—from hiring to task allocation—without proper oversight frameworks, they introduce unprecedented cybersecurity and operational risks...
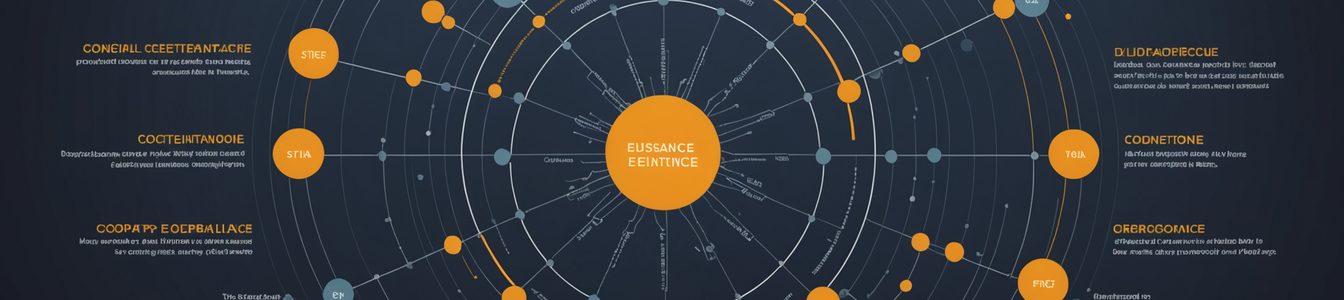
A convergence of recent reports from financial institutions, market indices, and governance studies reveals a critical and often overlooked threat vector: systemic cybersecurity vulnerabilities embedd...

The Canadian Centre for Cyber Security (CCCS) has issued a stark warning about the rapid integration of artificial intelligence tools by ransomware operators, marking a dangerous evolution in cyber th...