A disturbing new threat vector is emerging in the cybersecurity landscape, one that moves beyond financial loss to directly target human life. Recent cases in India, including a man blackmailed with m...


A disturbing new threat vector is emerging in the cybersecurity landscape, one that moves beyond financial loss to directly target human life. Recent cases in India, including a man blackmailed with m...

A surge of deeply discounted smartphones from retailers like Cdiscount, including models like the Xiaomi Redmi Note 14 and iPhone 14 Pro, is masking a significant cybersecurity threat. These gray mark...

The smart home ecosystem is undergoing a critical transformation phase where platform updates, new partnerships, and feature integrations are creating complex security vulnerabilities. Apple's final w...

A significant ransomware attack against the Royal Borough of Kensington and Chelsea (RBKC) council has caused widespread disruption to critical public services, demonstrating the cascading societal im...
The expanded strategic collaboration between operational technology (OT) cybersecurity leader Dragos and Microsoft marks a critical inflection point for critical infrastructure security. As industrial...

The global audit industry is facing a dual crisis that threatens the foundation of cybersecurity governance. On one front, major audit firms like the Big Four have dramatically reduced their client po...

French authorities have escalated a high-profile investigation into AI-generated deepfakes and harmful content on platform X, conducting raids on its Paris offices and summoning owner Elon Musk. The p...

Ambitious digital governance initiatives across Indian states like Andhra Pradesh, Karnataka, and Kerala are accelerating service delivery but operating within significant policy and cybersecurity voi...

The rapid integration of IoT and AI into disaster response and restoration industries is creating a new layer of critical infrastructure with profound cybersecurity implications. From AI-powered damag...

Recent incidents at educational institutions, including an unapproved group distributing religious materials at a Texas high school and new maritime school certification guidelines in the Philippines,...
Security researchers are tracking a coordinated surge in sophisticated phishing campaigns targeting users of major digital payment and subscription services. The attacks employ a dual-pronged strategy...

While VPNs are marketed as essential security tools for privacy and access, their widespread adoption introduces significant, often overlooked risks that expand an organization's digital attack surfac...

Amazon Web Services CEO Matt Garman has publicly dismissed the feasibility of space-based data centers, calling them "not economical" and "pretty far from reality." This statement represents a signifi...

A significant global shift is underway as judicial systems increasingly assume direct oversight of technical and cybersecurity compliance, moving beyond traditional regulatory bodies. From India's Hig...

The Police Service of Northern Ireland (PSNI) data breach saga has taken a dramatic turn, evolving from an accidental leak of officer rosters into a cascading series of privacy failures. In a stunning...
A sharp downturn in the cryptocurrency market is triggering a cascading crisis for publicly-traded companies holding significant Bitcoin and Ethereum treasuries. Firms like BitMine, Metaplanet, and M�...

Elon Musk's consolidation of xAI into SpaceX marks a pivotal moment in technology and security, creating a vertically integrated entity that controls critical infrastructure from space-based data cent...

Rapid advancements in artificial intelligence are triggering significant volatility in global financial markets, particularly impacting technology and IT service stocks. This AI-induced economic disru...

The smartphone industry's relentless pursuit of multi-day battery life through massive 7,500+ mAh cells is creating unforeseen physical security and safety hazards that extend beyond traditional cyber...
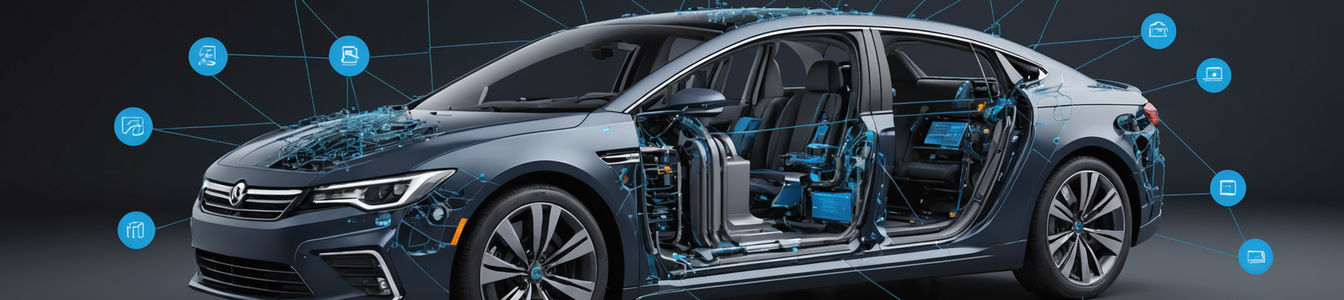
Major automotive manufacturers are rapidly expanding connected vehicle ecosystems through multinational IoT partnerships, creating complex new cybersecurity challenges. Hyundai Motor Group's recent al...