A massive credential leak exposing approximately 149 million passwords from major platforms like Gmail, Facebook, and Instagram has surfaced online, creating what security researchers are calling a 'c...


A massive credential leak exposing approximately 149 million passwords from major platforms like Gmail, Facebook, and Instagram has surfaced online, creating what security researchers are calling a 'c...

A disturbing trend is emerging where Internet of Things (IoT) devices, particularly connected cameras and sensors, are being deployed in sensitive private spaces without adequate consent or security. ...

The International Monetary Fund (IMF) has issued a stark warning about an impending 'AI tsunami' poised to disrupt global labor markets by 2030, with disproportionate impact on young professionals and...
A forensic audit of Telangana's Dharani land record portal has uncovered a major fraud scheme resulting in losses of approximately ₹3.95 crore (USD 475,000) in just two districts, with the state gov...

The emergence of multi-OS smartphones, exemplified by devices like the NexPhone capable of natively running Android, Ubuntu, and a mobile-optimized Windows variant, represents a paradigm shift in mobi...

A growing operational security concern is emerging as cryptocurrency hardware wallets are increasingly being mistaken for suspicious or dangerous devices by the public and law enforcement. Recent inci...

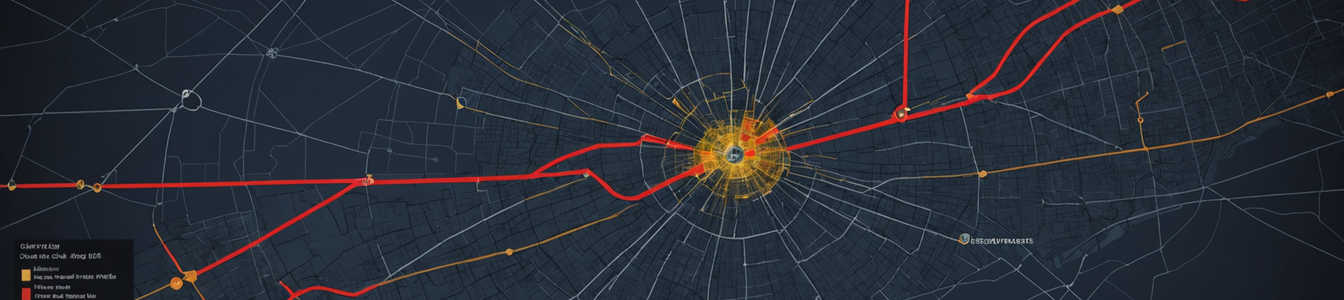
Recent analysis reveals sophisticated cross-border disinformation campaigns targeting South Asian nations, with coordinated media networks weaponizing information to shape geopolitical narratives. Ban...

The Indian rupee's depreciation to approximately 92 per US dollar is creating a dual-edged sword for the nation's cybersecurity ecosystem. While making internationally recognized certifications like C...
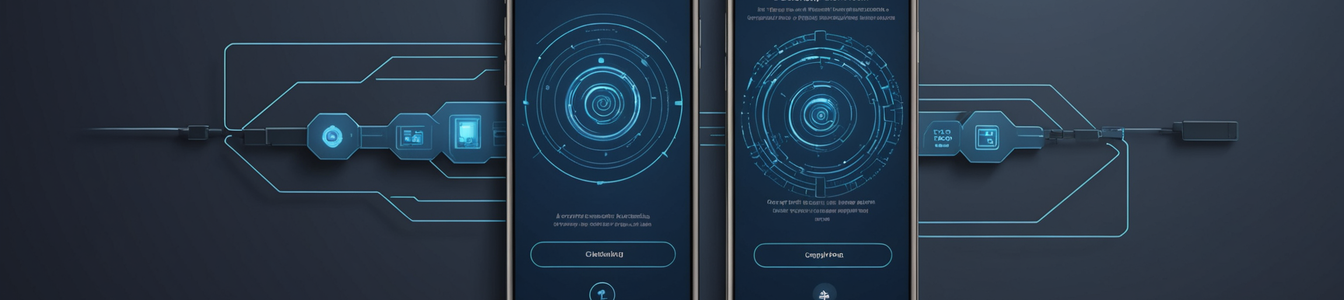
Google has announced a fundamental policy shift for the Android ecosystem, mandating developer verification for all sideloaded applications starting September 2026. This move represents Google's most ...

A growing segment of smart home consumers is deliberately choosing devices that operate entirely offline, creating a new security paradigm in consumer IoT. While eliminating cloud connectivity removes...

A perfect storm is brewing in the cybersecurity landscape, revealing dangerous gaps between perceived and actual security. A new investigation highlights how default VPN configurations often provide a...

A massive credential leak affecting 149 million accounts across major platforms including Gmail, Facebook, and Netflix has exposed fundamental weaknesses in current authentication systems. This incide...

India's Republic Day 2026 security deployment represents a paradigm shift in cyber-physical security operations, featuring the first operational use of AI-enabled smart glasses by security forces. Thi...

Cybersecurity researchers have uncovered a critical exposure: a 96GB database containing 149 million unique login credentials for major platforms like Gmail, Facebook, Instagram, Netflix, and OnlyFans...

The global VPN ecosystem is facing unprecedented pressure from both technical failures and geopolitical surveillance frameworks. A recent mass outage affecting Russian users attempting to bypass mobil...

A new global initiative called the Global Common Vulnerabilities and Exposures (GCVE) system has been announced, positioning itself as a potential successor or major evolution of the long-standing MIT...

The cybersecurity landscape for small and medium-sized businesses (SMBs) is undergoing a significant transformation driven by two converging trends: strategic bundling and aggressive price competition...

The rapid proliferation of smart Electric Vehicle (EV) charging infrastructure is creating a massive, centralized attack surface that threatens both the automotive and energy sectors. As highlighted b...

French cryptocurrency tax calculation platform Waltio has become the latest target of the notorious ShinyHunters cybercrime group, according to emerging reports. The group is allegedly threatening to ...

Modern mobile operating systems incorporate sophisticated privacy indicators like camera and microphone activity lights, yet these security features suffer from critical adoption and awareness gaps. R...