Google has implemented a selective rollout of client-side end-to-end encryption (E2EE) for its Gmail mobile applications on Android and iOS, restricting this enhanced security feature exclusively to e...


Google has implemented a selective rollout of client-side end-to-end encryption (E2EE) for its Gmail mobile applications on Android and iOS, restricting this enhanced security feature exclusively to e...

The enterprise authentication landscape is undergoing a fundamental transformation as passwordless technologies move from pilot projects to mainstream adoption. Driven by the convergence of FIDO stand...
A sophisticated, multi-front cyber offensive attributed to state-sponsored actors is targeting the foundational layers of global digital infrastructure. Security agencies are investigating a widesprea...
Parcel delivery scams are undergoing a dangerous evolution, moving beyond traditional SMS phishing to incorporate AI-generated voice messages and sophisticated multi-channel attacks. Security research...

A series of simultaneous physical disruptions at critical global ports, including a major fire at Singapore's PSA Pasir Panjang Terminal and a complete blockage at Europe's second-largest port in Antw...
The geopolitical instability surrounding Iran has triggered a global energy price shock with cascading effects far beyond critical infrastructure. Security Operations Centers (SOCs) are now facing unp...

The rapid proliferation of satellite internet for smart homes, IoT devices, and critical infrastructure is creating a new, centralized attack surface with profound security implications. As documented...

A federal judge has issued a preliminary injunction blocking Arizona's enforcement action against prediction market platform Kalshi, marking a significant escalation in the jurisdictional battle betwe...

The recent Molotov cocktail attack on OpenAI CEO Sam Altman's California residence marks a dangerous escalation in physical threats against AI industry leaders, directly linking public 'AI anxiety' to...

Recent quantum computing breakthroughs have dramatically compressed the timeline for securing blockchain networks against existential cryptographic threats. The Bitcoin Policy Institute warns that wha...

A critical maritime security crisis is unfolding in the Strait of Hormuz, where Iran's reported inability to locate its own deployed naval mines has created a persistent and unpredictable cyber-physic...

The global shift toward skills-based hiring is exposing dangerous fragmentation and inconsistency in background verification processes, creating significant cybersecurity and insider threat risks. As ...
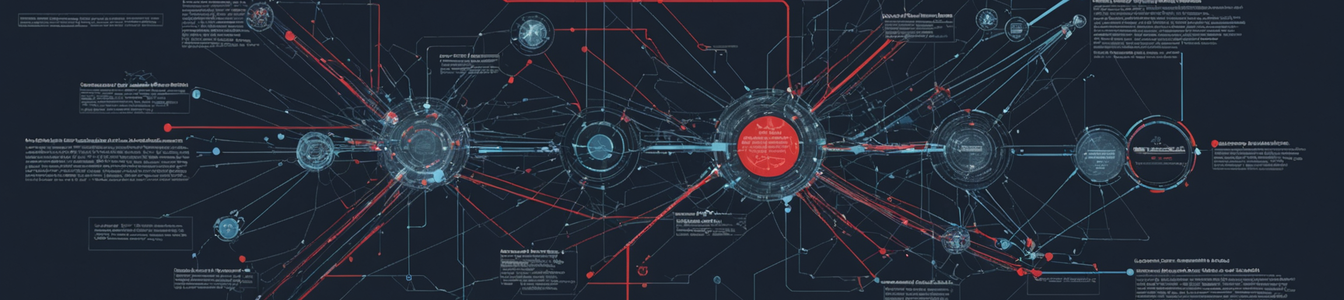
Microsoft's security researchers have uncovered a sophisticated new phishing campaign that represents a fundamental shift in attacker tactics. Instead of targeting user passwords, which are increasing...

Financial regulators and security officials across North America and Europe are convening emergency meetings following the preview of Anthropic's new 'Mythos' AI model, believed to represent a paradig...
Iran is reportedly implementing a bold strategy to collect transit fees from oil tankers passing through the Strait of Hormuz using Bitcoin and stablecoins. This geopolitical maneuver, framed as a 'to...

Anthropic's unreleased 'Mythos' AI model has triggered a critical debate in cybersecurity circles, with internal assessments reportedly concluding the system is too dangerous for public release due to...
A sophisticated supply chain attack has compromised the official website of CPUID, the developer behind the widely trusted system utilities CPU-Z and HWMonitor. Threat actors successfully breached the...
The cybersecurity landscape faces its most significant paradigm shift since the advent of ransomware, as Anthropic's decision to withhold its Claude Mythos AI model has triggered a global financial an...
A major investigation into West Bengal's teacher recruitment scandal reveals systemic corruption with far-reaching cybersecurity implications. The Enforcement Directorate's raids on former Education M...

Microsoft security researchers have uncovered a critical vulnerability in the EngageLab push notification SDK, a widely used third-party component integrated into thousands of Android applications. Th...