Multiple policy conflicts between Indian state governments and central authorities are creating inconsistent security frameworks and compliance challenges across critical sectors. Recent developments ...


Multiple policy conflicts between Indian state governments and central authorities are creating inconsistent security frameworks and compliance challenges across critical sectors. Recent developments ...

The Central Board of Secondary Education (CBSE) in India faced a significant public relations and trust crisis when QR codes embedded in national exam papers sparked viral misinformation. Intended as ...

An Iranian-linked hacking collective known as Handala Hack has been conducting a sophisticated three-year cyber espionage campaign targeting Western officials and institutions, according to recent inv...
Indian Oil Corporation (IOC) has issued a series of public reassurances regarding the uninterrupted supply of LPG, delivering approximately 2.8 million cylinders daily amid unspecified supply concerns...

The consumer IoT landscape is witnessing a strategic pivot from walled gardens to open platforms, exemplified by companies like Yarbo opening their robotics systems to third-party developers. This shi...
A convergence of geopolitical instability, supply chain disruptions, and escalating cyber threats is driving unprecedented demand for practical Digital Forensics and Incident Response (DFIR) training....

A dual-front consolidation of power in the AI ecosystem is creating unprecedented systemic security risks. Reports reveal Elon Musk leveraging his position in SpaceX's IPO to mandate banks purchase su...
A new wave of cyberattacks is targeting sensitive government data across continents, with two significant incidents highlighting the persistent threat to public sector digital infrastructure. In India...

A tragic accident in India's Nashik district, where a car plunged into an uncovered well killing nine family members, has triggered immediate political and regulatory responses including mandated safe...

A new wave of systemic trust failures is emerging beyond traditional financial and media sectors, now impacting critical areas including academic integrity, healthcare data, and personal biometrics. T...

A new generation of botnets is leveraging vulnerabilities in smartphone banking applications and low-cost IoT devices to create massive residential proxy networks. These sophisticated attacks compromi...

A series of ambitious urban development policies across Indian states—including Haryana's 'Stilt+4' and mixed land use initiatives, Delhi's slum rehabilitation with integrated e-rickshaw charging, a...

India's politically charged debate over the Central Board of Secondary Education's (CBSE) revised three-language formula is creating systemic risks for the country's cybersecurity talent pipeline. Whi...
The Uffizi Galleries in Florence, one of the world's most important cultural institutions, was targeted by a sophisticated cyberattack, prompting emergency security measures including the physical tra...

The hyperscale cloud providers are engaged in a multi-billion dollar arms race to capture the AI market, with Amazon alone reportedly planning $200 billion in data center investments. This unprecedent...

A severe shortage and price surge in DRAM and NAND flash memory components is triggering a fundamental shift in the mobile device landscape with significant cybersecurity implications. Major manufactu...

Recent incidents across the NFL, Hockey India, and healthcare reveal a systemic failure in personal conduct policy implementation that creates significant organizational security risks. The NFL's deci...

France's Ministry of Education is proposing to condition education subsidies on mandatory sexual violence prevention training for all school and extracurricular staff. While addressing a critical soci...
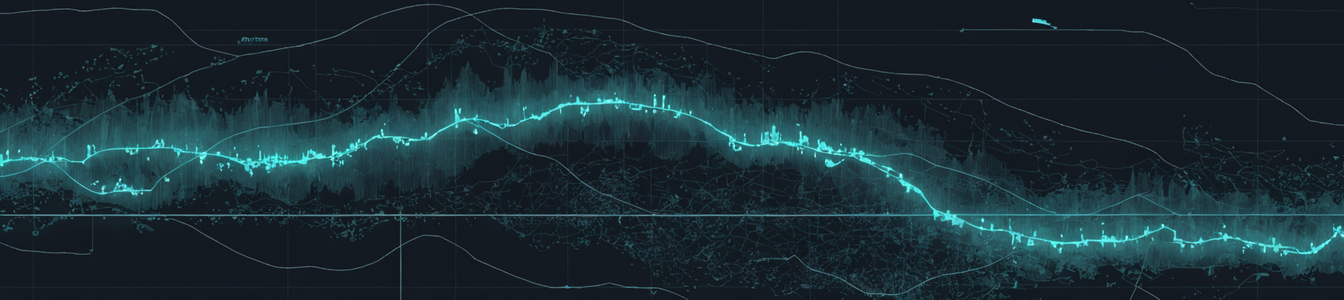
In response to escalating tensions and attacks in critical chokepoints like the Strait of Hormuz, global shipping is dynamically rerouting through unofficial, ad-hoc maritime corridors. This investiga...

The rapid evolution toward autonomous AI agent systems is creating unprecedented governance gaps that existing cybersecurity and content moderation frameworks cannot address. Anthropic's strategic mov...