A significant data leak at AI firm Anthropic has prematurely revealed details of its most advanced AI model to date, codenamed 'Claude Mythos.' Described internally as a 'step change' in capability, t...


A significant data leak at AI firm Anthropic has prematurely revealed details of its most advanced AI model to date, codenamed 'Claude Mythos.' Described internally as a 'step change' in capability, t...

A significant strategic security rift is emerging between the world's two largest blockchain ecosystems as the threat of quantum computing advances. Prominent industry analyst Nic Carter has highlight...

A convergence of legislative action and high-profile advocacy is forcing HR and L&D departments to confront the geopolitical dimensions of their technology choices. U.S. lawmakers are preparing legisl...

The global race for technological sovereignty is expanding far beyond semiconductors, creating new cybersecurity vulnerabilities and strategic dependencies. India is positioning itself as a critical s...
A global pattern of political transitions, leadership crises, and governance failures is creating systemic vulnerabilities that directly impact cybersecurity and operational resilience. From India's b...

Across critical sectors, reliance on antiquated, manual authorization processes is creating systemic vulnerabilities and operational bottlenecks. In a landmark shift, the U.S. Centers for Medicare & M...

A significant shift in the cyber threat landscape is underway, with attackers increasingly targeting email accounts as a single point of failure to bypass multi-factor authentication (MFA) and comprom...
Governments worldwide are increasingly deploying regulatory tools as active cybersecurity defenses, moving beyond traditional incident response. The U.S. Federal Communications Commission (FCC) has ta...

The cloud security landscape is undergoing a seismic shift as strategic, multi-year partnerships between hyperscalers, cybersecurity vendors, and AI specialists reshape the market. SentinelOne's expan...
A global race for AI chip sovereignty is fundamentally altering the geopolitical landscape and introducing new, critical dimensions to supply chain security. South Korea's strategic $166 million inves...

Bitcoin Depot, one of North America's largest cryptocurrency ATM operators, is navigating a severe operational and compliance crisis. The company has appointed former MoneyGram executive Alex Holmes a...
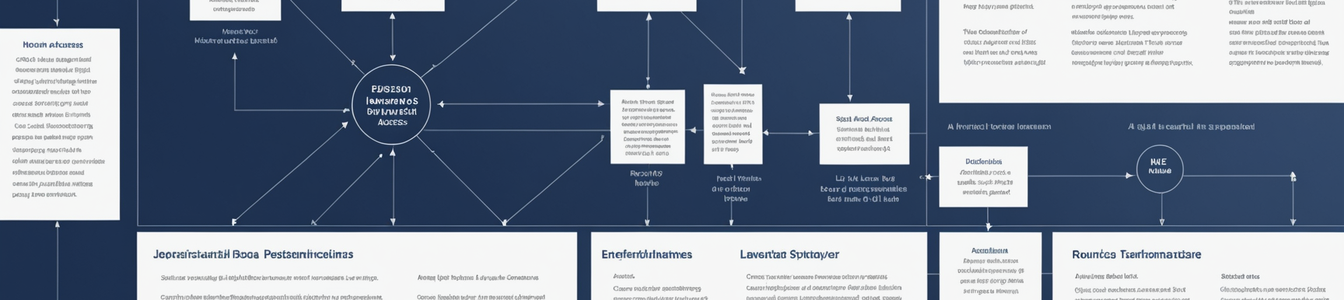
A global trend is emerging where traditional policy mechanisms—professional licensing, cross-border service regulations, and corporate authorization—are being leveraged to create de facto digital ...

In a significant week for international cybersecurity enforcement, authorities in Russia and Ireland have executed high-profile actions targeting critical nodes of cybercriminal activity. Russian law ...

The global logistics network, the backbone of modern commerce, is facing an unprecedented convergence of physical and cyber threats. Recent developments reveal a disturbing trend: the weaponization of...

National security and homeland defense operations are facing unprecedented strain from two simultaneous pressures: domestic political gridlock leading to government shutdowns and resource depletion, a...
The rapid deployment of AI systems for critical environmental and public safety monitoring—from wildfire prediction in the UK to crocodile detection in Australia and livestock management via 'AI col...

A wave of new sector-specific regulations targeting gambling, social media, professional licensing, and even retail sales is creating a complex and often contradictory compliance landscape with signif...

A series of recent U.S. federal court rulings has created significant legal uncertainty for cryptocurrency software developers, particularly those building non-custodial tools and privacy-focused appl...

Recent high-profile incidents involving star athletes and coaches—such as a Manchester United player caught speeding from the training ground days before a major transfer, and the departure of a Sin...

The rapid global expansion of blockchain-based payments and digital banking platforms is creating unprecedented systemic vulnerabilities. As financial infrastructure becomes increasingly digital-first...