A series of recent regulatory and judicial actions in India reveals a dangerous pattern where organizations use routine compliance filings to create an illusion of governance while systemic failures p...


A series of recent regulatory and judicial actions in India reveals a dangerous pattern where organizations use routine compliance filings to create an illusion of governance while systemic failures p...
As cryptocurrency markets face sustained pressure, institutional infrastructure players are making strategic moves that reveal both confidence and vulnerability. Anchorage Digital, the only federally ...
India's smartphone export surge, driven by government incentives and global supply chain diversification, is colliding with severe component shortages and market volatility, creating a perfect storm f...

A new multi-dimensional threat landscape is emerging where sophisticated cyber attacks targeting software supply chains converge with critical physical infrastructure vulnerabilities and geopolitical ...
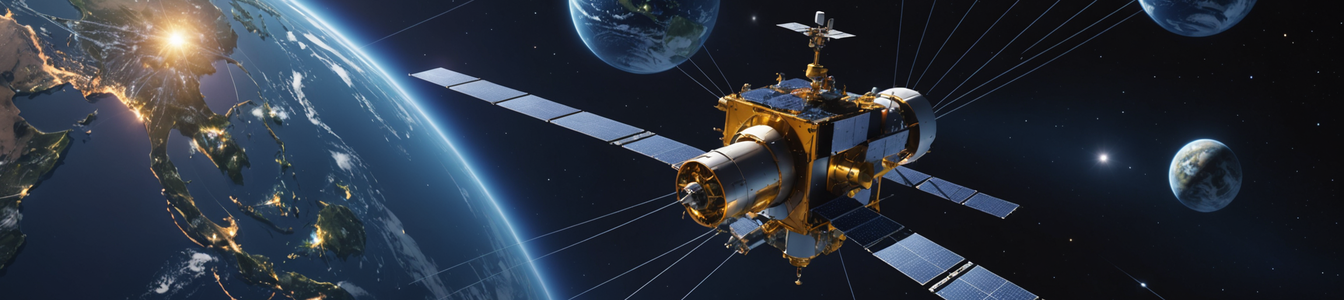
The rapid deployment of next-generation satellite IoT networks by companies like Iridium, Sateliot, and Rogers is creating unprecedented connectivity for global asset tracking, fleet management, and r...

A quiet revolution is reshaping the authentication landscape, moving beyond traditional passwords and one-time codes. Two distinct but complementary trends are emerging: telecom providers like Telin a...

Japanese regulators have conducted a surprise raid on Microsoft Japan's offices, investigating potential violations of the country's Anti-Monopoly Law. The investigation focuses on alleged restrictive...

A landmark lawsuit filed by Marquis against firewall provider SonicWall signals a critical shift in cybersecurity liability, moving the focus from end-user responsibility to vendor accountability. The...

The smart home market is facing a critical inflection point as major platform stagnation and strategic shifts create widespread ecosystem fragmentation. This analysis examines the growing security ris...
A recent aviation incident in India has exposed critical failures in regulatory oversight, revealing what cybersecurity professionals recognize as 'compliance theater'—where safety protocols exist o...

The explosive growth of artificial intelligence is colliding with aging and constrained power infrastructure, creating a critical national security vulnerability. Surging electricity demands from data...
India is pioneering a radical shift in cybersecurity workforce development through government-approved Apprenticeship Embedded Degree Programmes (AEDPs). This model, which integrates paid, hands-on in...

In a landmark operation, U.S. law enforcement has seized approximately $61 million in Tether (USDT) linked to a sophisticated 'pig butchering' romance investment scam, marking one of the largest crypt...

A critical governance gap is emerging as AI adoption accelerates in education and digital platforms, far outpacing institutional policy development. New data reveals 80% of students report AI improves...
A convergence of reports reveals a widening crisis in verification systems across financial, corporate, and geopolitical domains. While AI adoption in fraud prevention is accelerating, human fraud tea...

The U.S. Department of the Treasury's Office of Foreign Assets Control (OFAC) has imposed landmark sanctions against a Russian national, Artem Platonov, and his company, 'Operation Zero,' for traffick...
A concerning cybersecurity trend is emerging in the consumer electronics supply chain, where new, low-cost Android tablets are being shipped with dangerous malware embedded directly into their firmwar...

A new investigation reveals a systemic failure in social media advertising security, with nearly one-third of Meta ads in the EU and UK directing users to fraudulent, phishing, or malware-laden destin...

A significant shift is underway in how governments worldwide are combating Virtual Private Networks (VPNs). Moving beyond traditional technical blocking, authorities are now launching a coordinated le...

A seemingly innocuous DIY project to control a robot vacuum with a PlayStation controller spiraled into a global security incident, revealing critical vulnerabilities in popular smart home devices. Th...