A global pattern of regulatory and compliance directives failing to achieve on-the-ground enforcement is creating significant cybersecurity and operational risks. From ignored EV charging unit violati...


A global pattern of regulatory and compliance directives failing to achieve on-the-ground enforcement is creating significant cybersecurity and operational risks. From ignored EV charging unit violati...

The creative industries are facing a profound cybersecurity crisis as AI-generated content floods publishing pipelines, creating unprecedented supply chain vulnerabilities. Recent controversies, inclu...
A simultaneous market surge of deeply discounted refurbished smartphones and the announcement of advanced gaming hardware is creating a perfect storm for mobile security vulnerabilities. Major Europea...

A global pattern of abrupt, non-technical policy changes—from mandatory language requirements for transport workers to instant work-from-home transitions and streamlined travel procedures—is creat...

The global rush to reskill workforces in artificial intelligence is creating dangerous security blind spots, according to cybersecurity experts. While business schools like IIM Lucknow and institution...
The cryptocurrency custody landscape is undergoing a seismic shift as traditional financial institutions aggressively move to control self-custody infrastructure. In a landmark $70 million deal, tradi...

In a high-stakes ransomware standoff, video game giant Rockstar Games, developer of the Grand Theft Auto (GTA) series, refused to pay a ransom demand after a cyberattack. The criminal gang, identified...
Amazon Web Services has launched its Bio-Discovery AI platform, positioning itself as a critical player in pharmaceutical research by accelerating early-stage drug discovery through cloud-based AI. Wh...

The ongoing conflict in Iran is triggering a cascading series of economic crises far beyond the initial spike in fuel prices, creating new and complex threat vectors for cybersecurity and SecOps teams...
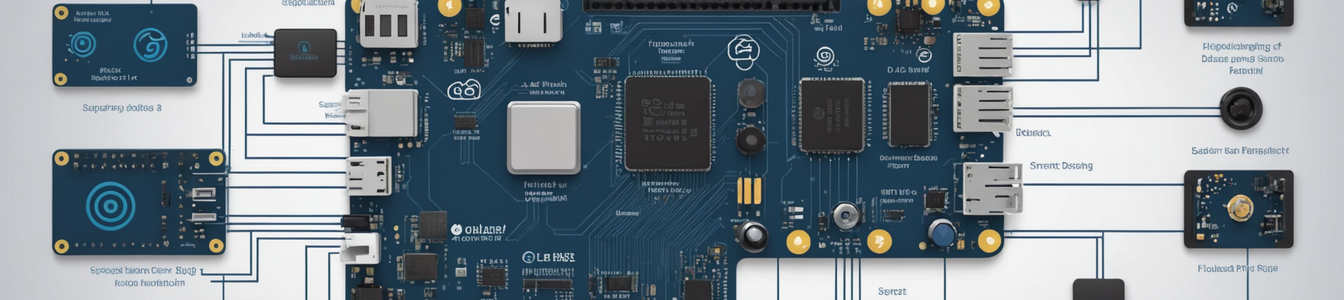
A growing consumer revolt against the complexity and fragmentation of mainstream smart home ecosystems is driving a surge in DIY solutions and alternative platforms. While this movement empowers users...

The explosive growth of artificial intelligence is triggering an unprecedented energy crisis that's transforming power grids into primary cybersecurity targets. As tech giants like Oracle secure massi...
In a counterintuitive turn of events, the recent data breach at Rockstar Games has resulted in a significant stock surge for parent company Take-Two Interactive, adding approximately $1 billion to its...
The Madras High Court's intervention in a case involving alleged discrepancies in the election affidavit and financial disclosures of Tamil Nadu's Deputy Chief Minister, Udhayanidhi Stalin, has escala...

A significant policy enforcement gap is emerging within government cybersecurity frameworks as top-down bans on specific AI models, like the reported restrictions on Anthropic's Claude Mythos, are bei...

A global trend of governments mandating mobile applications for essential services—from student exam results and fertilizer tracking to personalized insulin therapy—is creating an unprecedented an...

A new frontier in corporate security is emerging as executives begin developing AI clones of themselves for employee interaction. While these digital replicas promise efficiency, they introduce unprec...
The integrity of educational credentialing systems faces a dual assault this week, compounding an already critical crisis of trust. A significant new data breach has been reported at a national educat...

A fundamental shift is underway in how nations exert control over strategic resources, moving from physical permits to digital authorization systems that are becoming tools of geopolitical influence. ...
In a significant move to address the growing security blind spots created by unauthorized AI adoption, Cloudflare and Wiz have announced a strategic partnership. The collaboration aims to create a uni...
The commercial VPN market is undergoing a significant transformation as providers accelerate development of proprietary technologies to counter sophisticated censorship and evolving cyber threats. Key...